Simulation, Indistinguishability, and the Necessity of PKI
In the last article we discussed the possibility result for a protocol to satisfy consistency and liveness under a set of assumptions (Permission, synchronous, PKI), and we proved that no matter how many Byzantine nodes we have in the system, Dolev-Strong protocol always allows us to achieve consistency and liveness.
In this article, we will discuss the impossibility result in which there is no protocol that satisfies consistency and liveness with a set of faulty (Byzantine) nodes (: faulty node, : node)
1. The FLM Impossibility Result
1.1 Statement of the Impossibility Result
Theorem: In the synchronous model with , there is no Byzantine broadcast protocol that satisfies termination, agreement, and validity.
But wait! Didn't we just prove in the last article that Dolev-Strong protocol solves the Byzantine general problem no matter how many byzantine nodes we have in the system?
Yes, and neither of these proofs is incorrect or contradictory, the point is that each model uses a different set of assumptions that we will figure out throughout this lecture.
1.2 Intuition
Let's focus on the simplest use case of the impossibility result where and (: node, : faulty/Byzantine node)
We have 3 nodes Alice, Bob, and Carol. Each of the three nodes can communicate with the other two.
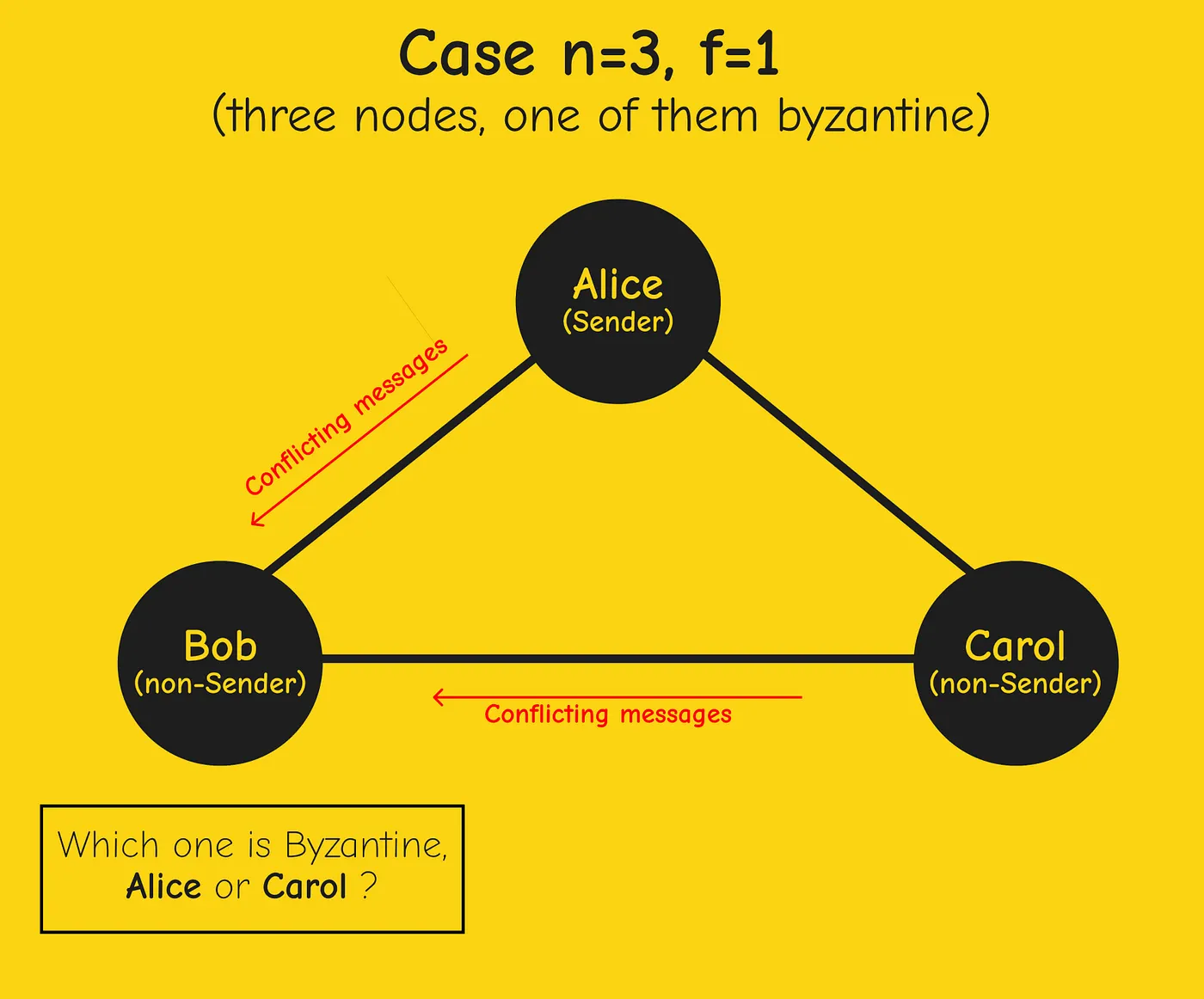
Let's assume that Alice is the sender, from point of view of Bob, he might hear conflicting messages one from Alice the sender, and the other from Carol (non-sender). Bob knows that one of the nodes is Byzantine but he has no idea which one. One scenario might be that Alice is sending conflicting messages to both Bob and Carol, or the other scenario where Carol is attempting to frame what she heard from Alice.
Think of the case where we have and , in this case, Bob could figure out the right output by using the majority vote of the three other nodes, whereas in the case of we have a problem.
2. The FLM Proof of Theorem
Let's prove the theorem by contradiction.
We assume that the theorem is false, and in fact, there's a protocol (we call it ) for the Byzantine broadcast problem with and .
If we can derive a contradiction from this we completed the proof. (The protocol could be any arbitrarily crazy event-driven piece of code, we don't care)
The Hexagon
The Fischer-Lynch-Merritt (FLM) proof is a genius step to prove the result of this theorem.
We're going to buy 6 nodes, three nodes for Alice, Bob, and Carol, and the other three are copies of each of the first three nodes. Then we run the protocol on each of them.
There are 3 things we expect to be known first for a node before firing the protocol :
- If node is the sender, its private input
- Among node and the two other nodes, which one is the sender
- The IP address of the two other nodes
Buy node A and set it up with the following 3 initializations as mentioned above:
- A neighbors are B and C (A knows B and C IP addresses);
- A is a sender while B, and C' are non-senders;
- A private input is 0.
- B neighbors are A and C' (B knows A and C' IP addresses);
- A is a sender while B, C' are non sender;
- C neighbors are A and B' (C knows A and B' IP adress);
- A is a sender while B, and C' are non senders;
- A' neighbors are B' and C' (A' knows B' and C' IP address);
- A' is a sender while B', and C' are non-senders;
- A private input is 1.
- B' neighbors are A' and C (B' knows A' and C IP addresses);
- A' is a sender while B', and C are non-senders;
- C' neighbors are A' and B (C' knows A' and B IP addresses);
- A is a sender while B, and C' are non-senders;

Proof Strategy
Let's assume we have a protocol that satisfies validity and agreement for and . Now, remember it's not accurate to say that agreement and validity carry over the thought experiment where we have 6 nodes.
Our goal is to derive a contradiction from the protocol .
We're not going to use these assumptions on the thought experiment (6 nodes Hexagon), because we don't know even what validity and agreement mean in 6 cycles. So we need to come up with some bonafide of the Byzantine Broadcast with only 3 nodes.
Proof: Scenario #1
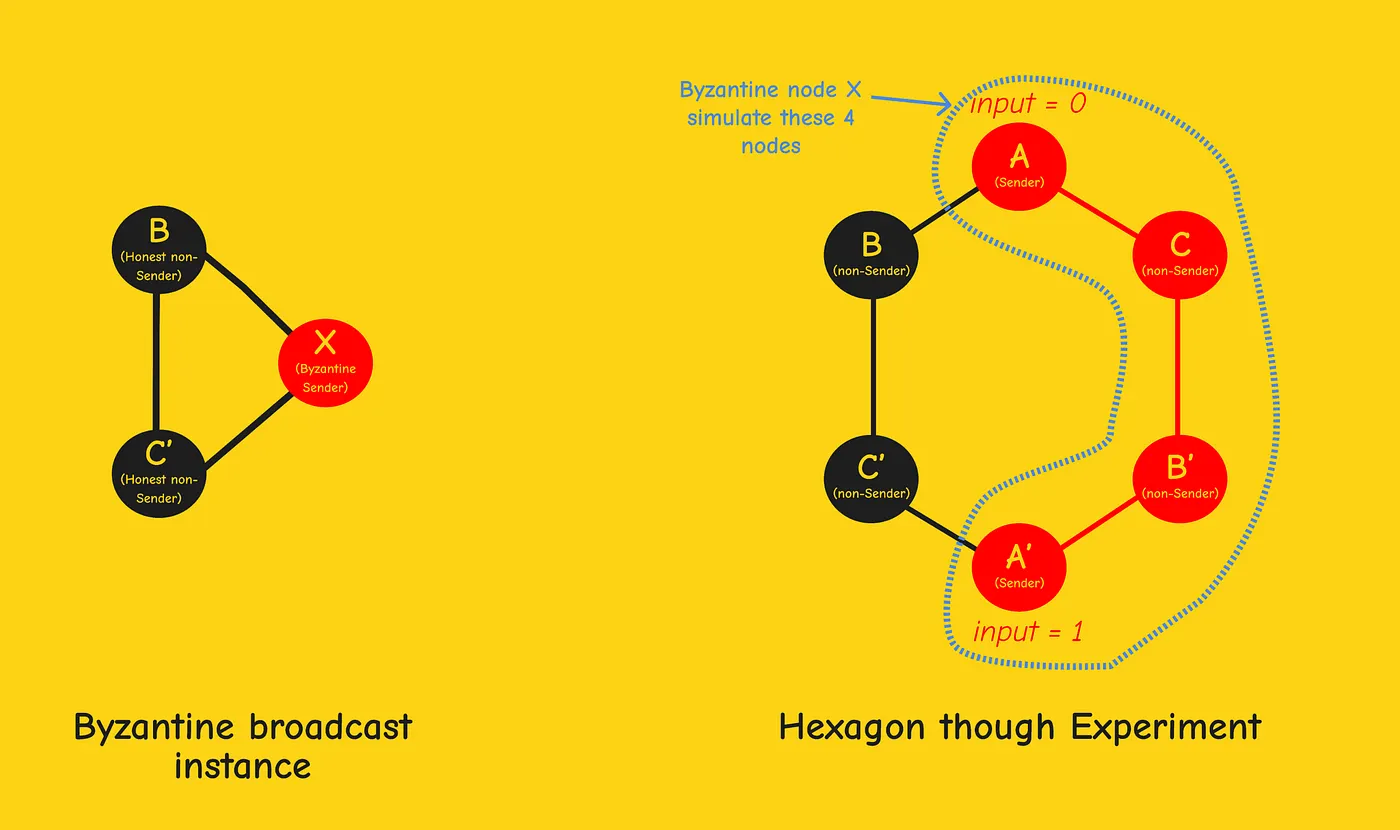
In scenario 1 we have and are non-senders that are running the protocol , and is a byzantine sender that can do whatever it wants.
Strategy for node : simulate the behavior of the four nodes by setting up four local virtual machines, each running protocol with the appropriate initialization.
So communicates with as if it were in the hexagon, and communicates with as if it were .
The point is to keep the honest nodes and in the dark. They cannot distinguish which is the actual reality and must operate the same in both cases.
Result 1: Since satisfies termination and agreement, nodes and output the same value (no matter the strategy used by ) in the triangle and in the hexagon.
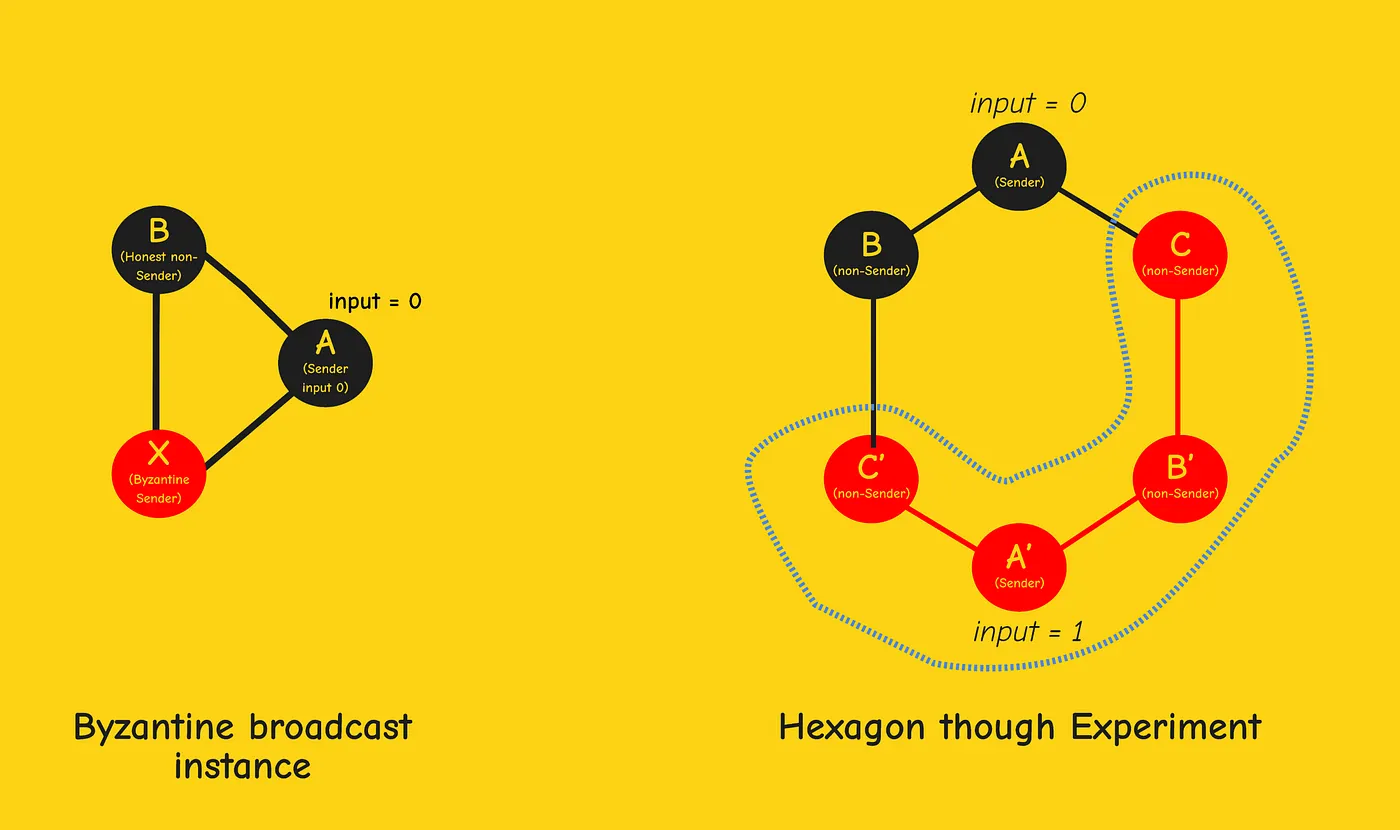
Proof: Scenario #2
Strategy for node : simulate the behavior of the four nodes .
Result 2: In this case is an honest sender, using the validity property, and should both output ('s private input). and are kept in the dark. They don't know if they are running in a triangle or a hexagon with 6 nodes.
Proof: Scenario #3
The third scenario is similar to the second one, with an honest sender with private input .
Strategy for node : simulate the behavior of the four nodes .
Result 3: In this case is an honest sender, using the validity property, and should both output ( private input).
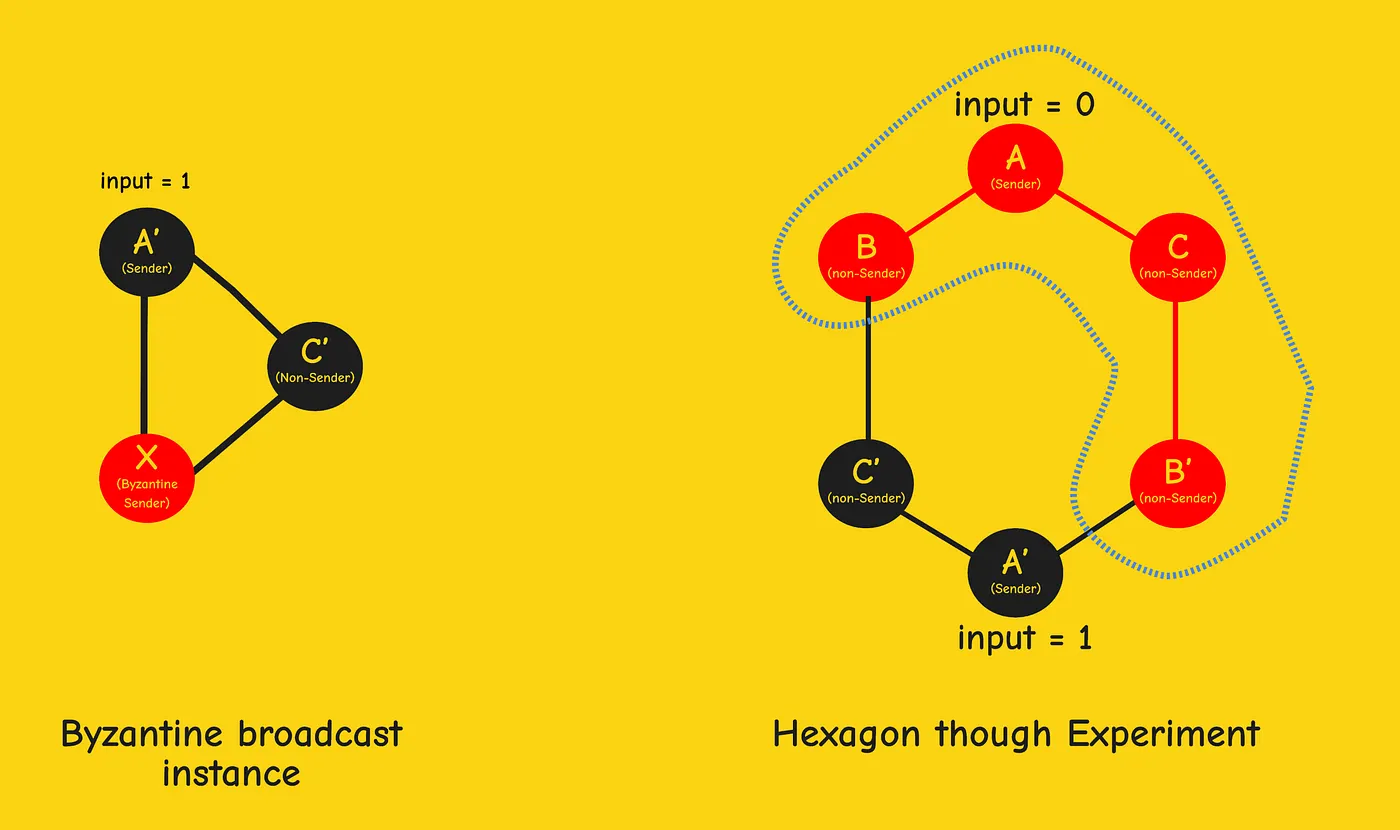
Conclusion
These 3 results assert that nodes and must terminate and output the same value (from result 1); must output (from result 2); must output (from result 3).
This concludes our contradiction since the experiment can't possibly satisfy these three mutually inconsistent constraints at the same time.
This implies that the assumed protocol cannot exist. That is, there cannot be a Byzantine broadcast protocol with and that guarantees termination, agreement, and validity.